What is multi-factor authentication?
Multi-Factor Authentication (MFA) verifies a user’s identity by requiring multiple credentials.

Mar 14, 2022
MFA provide enhanced security to your systems. Traditional usernames and passwords can be stolen, and they are vulnerable to brute force attacks. MFA creates additional layers of security to help increase the confidence that the user requesting access is actually who they claim to be.
Examples of Multi-Factor Authentication include authentication through:
- Codes generated by smartphone apps
- Badges, USB devices, or other physical devices
- Fingerprints
- Codes sent through SMS or email
- Facial recognition
Set up MFA for Atlassian
Kantega SSO Enterprise allows you to setup MFA and protect against unauthorized access to Jira, Confluence, Bitbucket, Bamboo and FeCro (server and data center). It is the responsibility of the identity provider (ex. AzureAD, AD FS, Okta, GSuite, and many more) to request and verify user credentials and do the actual MFA. But at the same time, it is important that backdoors to traditional login mechanism in the Atlassian systems are closed. You typically do not want to find and use traditional and less secure login mechanisms when stronger authentication should be enforced.
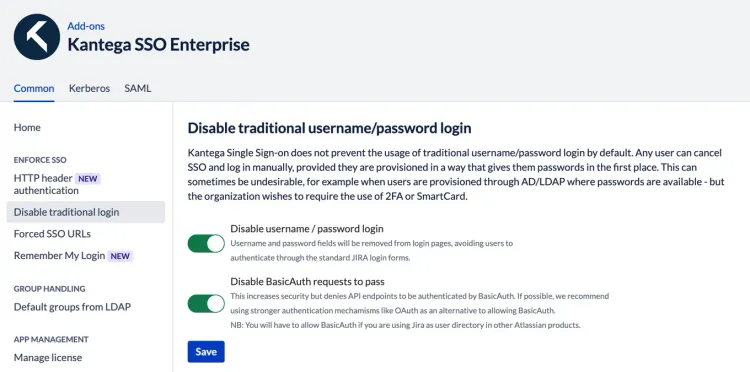
The screenshot above shows how you easily can disable tradional login dialogs and also disable all basic auth requests at the server level. The first toggle allows you to remove username and password fields from login pages, avoiding users to authenticate through the standard login forms. The second toggle increases security further by denying API request to be authenticated by BasicAuth.